Cloud Penetration Testing
Cloud Penetration Testing is the process of detecting and exploiting security vulnerabilities in your cloud infrastructure by simulating a controlled cyber attack. Cloud pentests are conducted following strict guidelines from cloud service providers such as Amazon Web Services and Google Cloud Platform. Pentesting is the process of identifying security vulnerabilities in a system, service, or network. In essence, cloud penetration testing is simply simulating an attack on your cloud services in order to determine their security.

Why Cloud Penetration Testing Is Important ?

A Cloud Penetration test uncovers vulnerabilities residing within your cloud infrastructure and provides a detailed attack narrative to help evaluate the impacts of each finding.
Determine what an attacker could do with valid access keys or tokens. Compare current cloud configurations against security best practices. Go beyond a vulnerability assessment to identify the techniques attackers would take to breach sensitive information.
Strengthen your cloud infrastructure with an expert. Cloud pentesting is new and needs a pentester with specialized training.
Cloud Penetration Testing Benefits
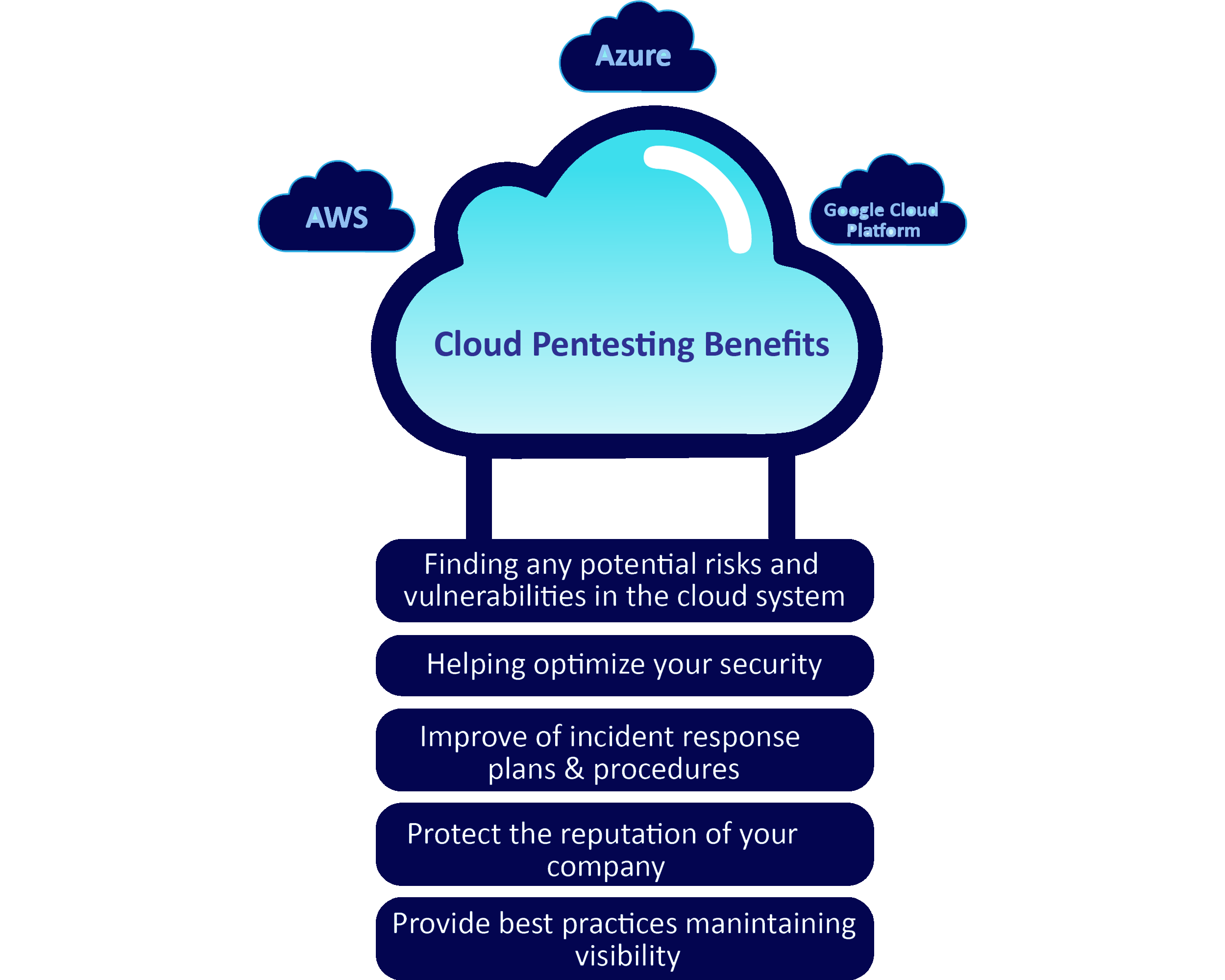
- Scale with improved visibility.
- Design with security standards.
- Deeply integrated services.
- Productivity with a secure ecosystem.
- Induce confidence in customer.
- Take advantage of security.
- High availability and support.
Cloud Penetration Testing Methodology
Security professionals engaged in cloud penetration testing will typically examine three areas of scope: the cloud perimeter, internal cloud environments, and on-premise cloud management, administration, and development infrastructure.
The Stages of Cloud Penetration Cloud penetration testing often takes place in three stages—evaluation, exploitation, and remediation.
- Misconfigurations
- Data Breaches
- Malware/Ransomware
- Vulnerabilities
- Advanced Persistent Threats (APTs)
- Supply Chain Compromises
- Poor server configuration
- Insider Threats
- Weak Identities and Credentials
- Insecure Interfaces and APIs
- Inappropriate Use or Abuse of Cloud Services
- Shared Services/Technology Concerns
Cloud penetration testing can help prevent these most common types of cloud security threats:
Why Choose Mighty ?
- Professional Expertise
Mighty's security research team consists of expert security researchers who have had an extensive track record of finding security vulnerabilities in a diverse range of widely recognized companies and organizations.
- Mighty Coverage
Our aim is to provide our clients with only high quality penetration testing services that cover every aspect of their applications in order to meet their requirements. The purpose of this is to protect their business and their users' data from being misused by malicious individuals.
- Debrief Report
Our penetration testing reports provide companies with clear, precise and descriptive recommendations for remediation. This will make it easier for developers to reproduce and resolve vulnerabilities.
- Support
Our team works closely with the companies to understand and mitigate the discovered security vulnerabilities.

Your business is your future, so secure it.
Book a free consultation with one of our security specialists to discuss the details of
your cyber security requirements.