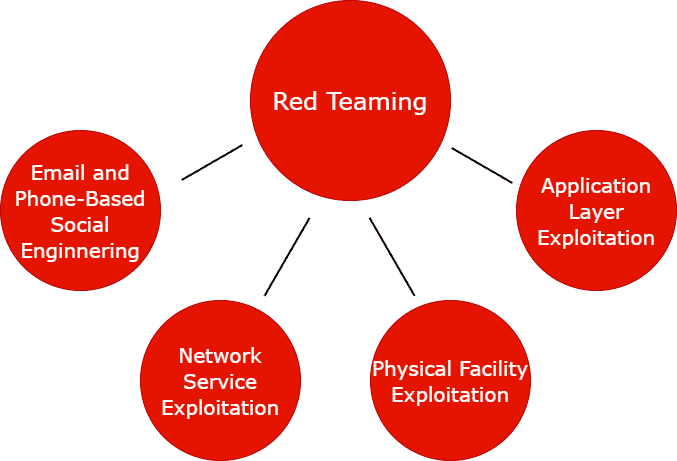
Red Teaming
Red teaming is a stealthy procedure that often aims to test not only the systems and protocols in place, but also the people who manage them. Red teaming is a focused, goal-oriented security testing method that is designed to achieve specific objectives. If the objective of a red team is to access a sensitive server or a business-critical application, its success will be measured by how well it can accomplish this objective. If the red team achieves its goal, then the organization is insufficiently prepared to prevent such an attack. Of all the available cyber security assessments, a simulated cyber-attack is as close as you can get to understanding how prepared your organisation is to defend against a skilled and persistent hacker.
Why Red Teaming Is Important ?

Of all the available cyber security assessments, a simulated cyber-attack is as close as you can get to understanding how prepared your organisation is to defend against a skilled and persistent hacker. The main differences between red teaming and penetration testing are depth and scope. Pen testing is designed to identify and exploit as many vulnerabilities as possible over a short period of time, while red teaming is a deeper assessment conducted over a period of weeks and designed to test an organisation’s detection and response capabilities and achieve set objectives, such as data exfiltration.
As part of Mighty's Red Team Operations, we rigorously test the effectiveness of technology, personnel, and processes over an extended period of time in order to detect and respond to highly targeted attacks.
Red Teaming Benefits

- Evaluate your response to attack.
- Identify and classify security risks
- Uncover hidden vulnerabilities
- PAddress identified exposures
- Prevent reputational loss
- Enhance blue team effectiveness
- Prioritise future investments
Red Teaming Methodology
As part of Mighty's red team assessments, we use real-world adversary techniques to compare the systems under test against the tools and techniques of real adversaries. Red teaming is a methodology used to assess an organization's security by simulating an attack; and it's an indicative of a strong cybersecurity culture.
In a red team scenario, the experts will use different tools and techniques to imitate an actual attack to determine how vulnerable your company is to this type of situation.
- A hacktivist exploits a vulnerability to sabotage the industry's infrastructure and delay production.
- A malicious employee with privileges deploys malware in the system to ruin several machines.
- A hacker uses social engineering to fool an employee, get credentials to access a robust database, and expose that information.
- A cybercriminal exploits unpatched network services to access sensitive information about clients.
Examples Of Red Team Scenarios:
Why Choose Mighty ?
- Professional Expertise
Mighty's security research team consists of expert security researchers who have had an extensive track record of finding security vulnerabilities in a diverse range of widely recognized companies and organizations.
- Mighty Coverage
Our aim is to provide our clients with only high quality penetration testing services that cover every aspect of their applications in order to meet their requirements. The purpose of this is to protect their business and their users' data from being misused by malicious individuals.
- Debrief Report
Our penetration testing reports provide companies with clear, precise and descriptive recommendations for remediation. This will make it easier for developers to reproduce and resolve vulnerabilities.
- Support
Our team works closely with the companies to understand and mitigate the discovered security vulnerabilities.

Your business is your future, so secure it.
Book a free consultation with one of our security specialists to discuss the details of
your cyber security requirements.